Imagine a technology that could undo all encryption on the internet. It would be impossible to trust any information communicated, impossible to verify any identity. The security of our society and our economies would crumble.
That’s the potential threat posed by future quantum computers. For all the good that quantum computing promises — eradicating disease, helping us understand climate change, identifying new molecules and materials — in the wrong hands it could pose an existential risk to classical computers and existing technologies. Fault-tolerant quantum computers with enough processing power would be enough to unravel all the cryptography used in the modern internet.
This threat is especially relevant when it comes to blockchain. More and more companies are adopting blockchain technology given the transparency, security and reduced costs. 84% of companies had some involvement in blockchain in 2018. Quantum threatens the very fabric of the distributed ledger, with the ability to break everything the secure, decentralised, transparent networks stand for.
The strengths — and weaknesses — of blockchains
Quantum computing won’t destroy blockchains themselves. It instead threatens to break the security features that underpin them; the features which make it the unique and trusted network it is today.
As public data structures that rely heavily on cryptography, blockchains are natural targets for hackers looking to exploit cryptographic vulnerabilities. Whether it’s a public chain used to send, verify and receive cryptocurrency, or a private version built for business, each one relies on blocks of data placed one after the other. For data to be included in this chain, it needs to be added and then verified by other members of the group.
Take the example of a private enterprise blockchain. When one company wants to move assets to another company they put the transaction on a block and add this block to the chain. Other members of the community look at the block, confirm that the correct value has gone from company A to company B and they verify the transaction. Once it’s added, this transaction (or any flow of data) is locked into the chain for life. It's kept not only for posterity, but so that everyone involved knows exactly where that data has come from. The latter is particularly useful for supply chains or tracking the sources of ingredients in food or materials in devices.
On the plus side, this process means the entire history is preserved, locked and protected. On the other hand, it means that the entire history and its security is dependent on the last block placed. If a criminal were to bypass this security and transmit a fraudulent block, every point forward would be based on a modified version of history. Or worse, blockchains could 'fork', with different parties holding different versions of the past. It would be unclear which parties owned valuable assets, potentially allowing criminals to steal what isn’t theirs.
This is bad enough when the data held on blockchain is financial, let alone as the technology is adopted by health providers, governments and even used to underpin the digital data of entire countries — all routes that could be, and are being, explored.
How quantum breaks the chain
In its current form, the security used to protect each of these blocks is robust and resistant to traditional cracking methods. Yet it’s facing a significant threat; one that has already been proven — the threat of quantum-based algorithms. These algorithms can and will break such keys, and they will eventually do so with relative ease. This means it’s only a matter of time before robust quantum computers currently under development will be able to break larger and larger keys. Some estimates place this moment as little as five to 10 years away.
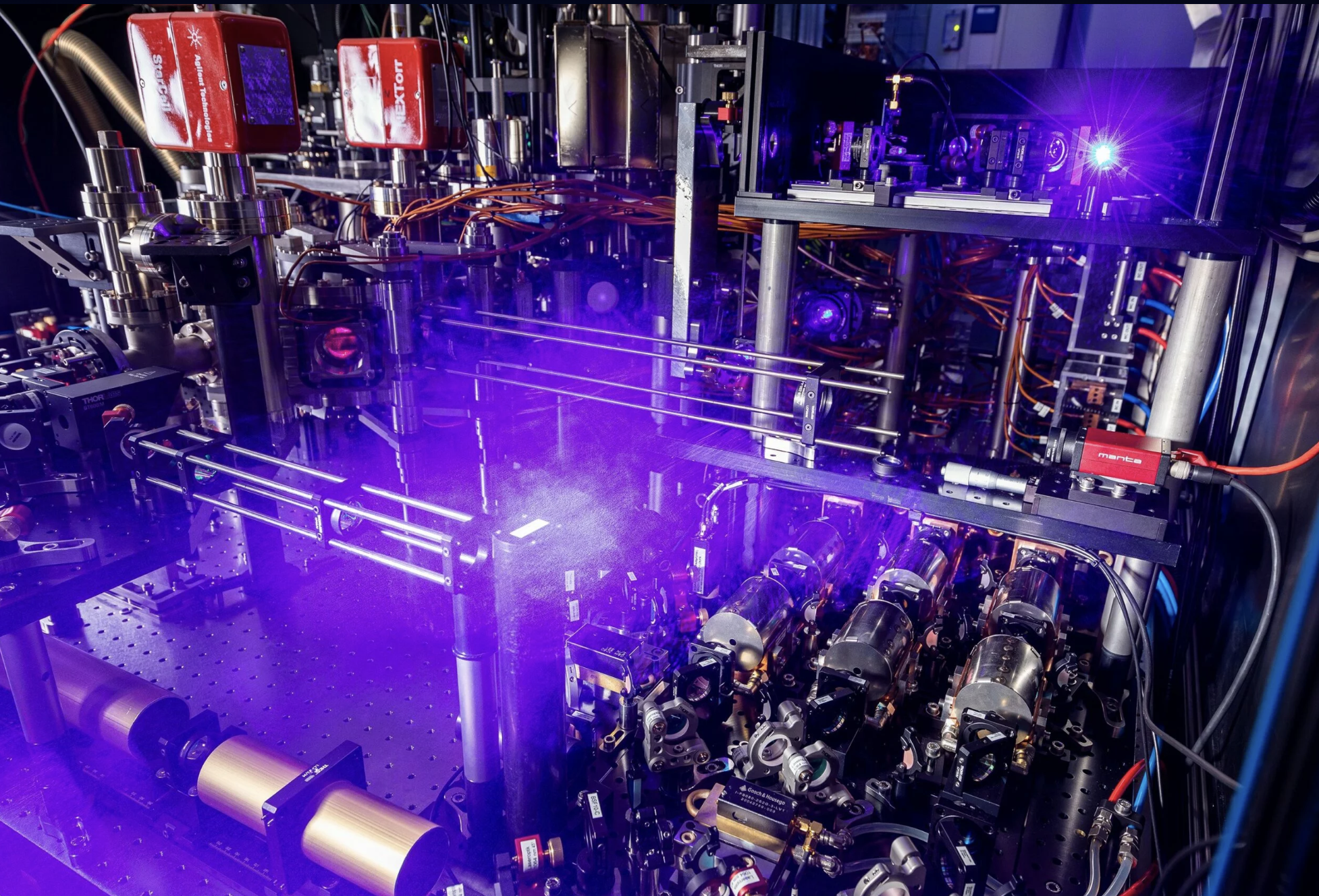
The only way to keep blockchains safe is to protect them with quantum-proof cryptographic keys in the first place; keys that are impenetrable from even the fastest, most advanced quantum computers we can envision today. To fight quantum with quantum.
The only way to keep blockchains safe is to protect them with quantum-proof cryptographic keys in the first place...To fight quantum with quantum.
In a paper, published this month with the Inter-American Development Bank (IDB) and Tecnológico de Monterrey, we have developed a proof-of-concept that can be built as a layer on top of existing blockchain technologies. This layer relies upon CQC’s IronBridge Platform to generate provably-perfect, quantum-proof keys that address two particular areas of weakness uncovered in blockchain technology. These are the internet communications between blockchain nodes, and blockchain transaction signatures used by businesses to verify their identity when submitting transactions or validating blocks.
By 'quantum-proof', we refer to keys that are generated using quantum computers, harnessing the innate randomness of quantum mechanics. Not only are these keys completely unpredictable to a quantum attacker, but they are also based on algorithms that are believed to be unbreakable by quantum computers. This technology, available through the IronBridge platform from CQC, works today, even on the limited quantum computers that currently exist, and without ever interfering with a blockchain’s functionality. It represents the first time ever such a solution has been built and proven in this way.
Yet because securing a blockchain involves applying the same remedies as for other technologies, the work we’ve done here is not unique to blockchains. It has vast potential.
However, the system is not perfect. It’s far more efficient for quantum cryptography to be built into the very bones of blockchain technology, rather than layered on top. It is hoped this research encourages blockchain vendors towards earlier adoption of quantum-proof algorithms and key generation.
Others are approaching the quantum cybersecurity threat in different ways. Companies such as British Telecom and Toshiba are exploring how to share keys using quantum physics; a process known as quantum key distribution (QKD). These QKD systems are still in their infancy, with many technical challenges ahead, but they show promise as another area where quantum will strengthen cybersecurity.
The threat posed to blockchains by quantum computing isn’t new, nor is it something that’s going to hit in the next few months. But every baby step we take towards faster, cheaper quantum computers today is bringing it more starkly into view. It may be five years from now, it could be 15, but the sooner we protect blockchains and get the basics right today, the more protected it — and us — will be in the future.